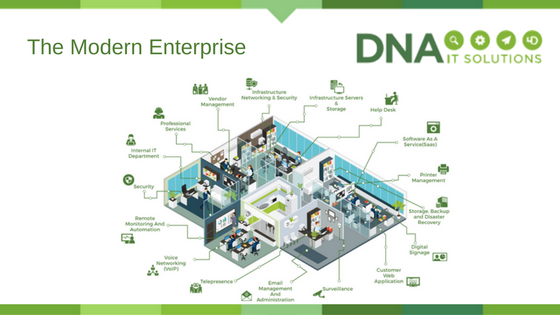
The modern office looks a lot different than it did the last time a law was passed on data protection.
We now use more mobile devices in our work and personal life. Company data is no longer just stored with the walls of an office as we move towards storage in the cloud.
With personal data breaches quite common, this not only puts people at risk of identity theft and financial loss but also puts businesses at risk of losing customer confidence. Now that GDPR is being introduced next year the consequences will be even more severe with hefty fines.
Sophos recently published a whitepaper on the subject and you can read the full version here. DNA IT Solutions partner with Sophos to provide an all-round solution to business IT Security and we felt it would be useful to share some of their insights with you.
Why are the changes needed?
It was recognised that there was a need to address the protection of data due to the major technological developments in the past 20 years. GDPR takes the form of a regulation, meaning that it applies directly in every member state in the form in which it was passed. The regulation is intended to strengthen the privacy rights of EU citizens, restore confidence in online activities and better protect customer data by requiring companies to adopt new data protection processes and controls.
Significant elements of reform
GDPR addresses the security of processing data and how organisations need to implement appropriate security measures to protect personal data. It makes specific reference to ‘encryption of personal data’ as one of the means to achieve this. In regard to encryption technology, this means having a robust key management procedure in addition to encrypting your data. The wider implications are having a sound disaster recovery plan in place.
The consequences
Failure to comply could mean files of up to €20million or 4% of the total turnover whichever is higher. If you don’t put the right technology in place to protect personal data, then you may have to pay – directly to the supervisory authority and indirectly from reputation damage, and loss of goodwill and customer trust. However, companies that encrypt their data protect their customers and themselves.
How Sophos helps you meet the data protection challenge
A solid data protection strategy isn’t built in a day. But consider that 57% of data breaches are due to hackers or malware and 23% of data breaches are caused by unintended disclosure (human error). Securing against these threats is a great place to begin and Sophos recommends three steps to achieve it.
- Stop the top causes of data loss
Malicious attacks and accidental loss or theft are two major causes of data breaches. Sophos Central Device Encryption is the easiest way to manage full disk encryption for all your PCs and Mac computers centrally. Full disk encryption is the most basic form of encryption and it’s widely recommended that all computers use it to protect data at rest. It will keep your data secure in the event that a device is lost or stolen. Sophos Mobile extends similar protection to data on your mobile devices.
Sophos Intercept X works alongside your existing antivirus protection to provide advanced anti-malware, anti-exploit and anti-ransomware protection – keeping you safe from the latest data-stealing attacks.
- Stop threats at the door
With todays’ increasingly sophisticated and aggressive malware attacks, having a multi-layered security setup that can stop attacks at every level of your network is essential. XG Firewall protects your network devices by stopping these attacks at the perimeter, before they get to your devices.
Sophos Email Appliance automatically blocks or encrypts sensitive emails and attachments (e.g. PDFs) ensuring your data is always protected, and suspect emails are stopped before they reach your users’ inboxes.
- Stop human error
Most of us have sent an email to the wrong person at some point. But when sensitive data is involved that innocent mistake can become a costly fine. The file-level encryption delivered by Sophos SafeGuard means that even when data leaves your devices or network (e.g. email attachment, cloud storage) it stays protected – so even if you suffer a data breach the chance of a fine is greatly reduced.
DNA IT Solutions have already put in place many of the measures that Sophos refer to for our clients. If you want to find out more about how Sophos can protect your business, please get in touch with us today.