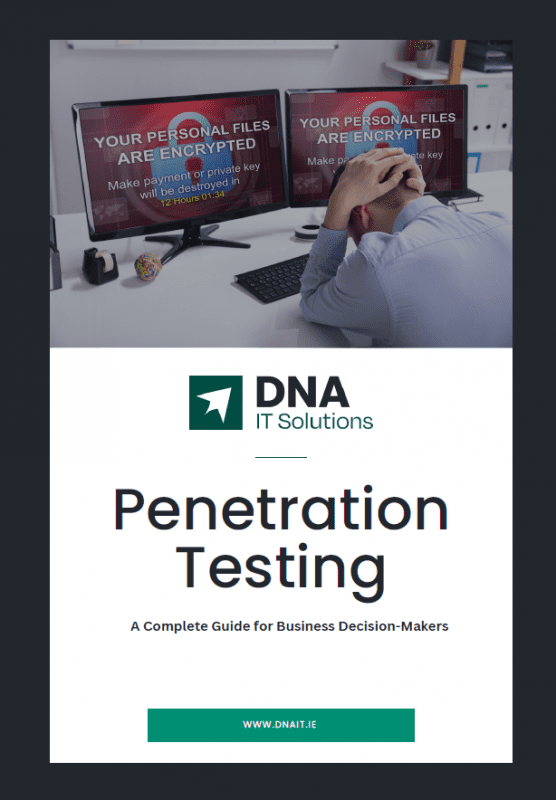
Penetration Testing
Request a Consultation
A penetration test simulates a real-world cyberattack on your systems. Our certified security professionals use the same tools and techniques as actual attackers, identifying weaknesses before criminals do.
Get in touch today and take the first step to a more secure infrastructure for your business.